Quantum computing presents a significant challenge to conventional encryption methods. Its advanced algorithms, such as Shor’s algorithm, can compromise widely used systems like RSA and ECC. This vulnerability necessitates a shift towards quantum-resistant encryption techniques. As organizations navigate this evolving landscape, the urgency to adopt robust security measures becomes paramount. The implications of this transition raise critical questions about data security in a quantum-dominated future.
The Basics of Quantum Computing and Encryption
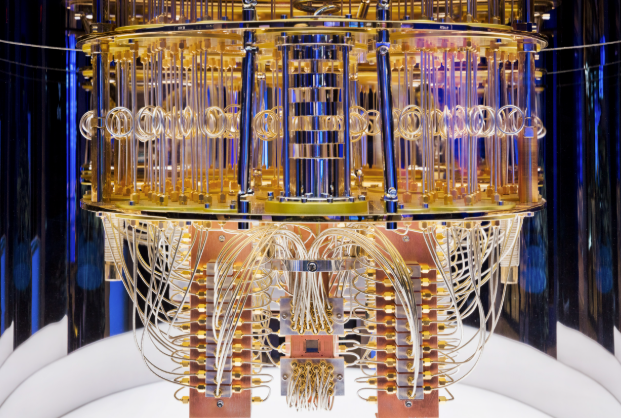
As quantum computing continues to evolve, its implications for encryption become increasingly significant.
Quantum bits (qubits) differ fundamentally from classical bits, enabling complex calculations at unprecedented speeds. This capability allows quantum computers to perform tasks that classical systems cannot achieve efficiently.
Consequently, the foundational principles of encryption, reliant on classical bit manipulation, face profound challenges, necessitating a reevaluation of data security methodologies in a quantum-dominated landscape.
How Could Quantum Computing Break Current Encryption Methods?
The advent of quantum computing poses a significant threat to existing encryption methods, particularly those based on widely used algorithms like RSA and ECC (Elliptic Curve Cryptography).
Quantum algorithms, such as Shor’s algorithm, exploit cryptographic vulnerabilities by efficiently factoring large integers and solving discrete logarithms, undermining the security foundations of traditional encryption.
Consequently, this technological advancement necessitates a reevaluation of current cryptographic practices to safeguard data integrity.
Emerging Quantum-Resistant Encryption Techniques
While traditional encryption methods face vulnerabilities from quantum computing, researchers are actively developing quantum-resistant encryption techniques to fortify data security against these emerging threats.
Among these advancements are post quantum algorithms, which leverage mathematical structures robust against quantum attacks.
Lattice-based cryptography, in particular, shows promise due to its complexity and resistance, ensuring that sensitive information remains secure in a post-quantum world.
See also: How Quantum Computers Differ From Classical Computers
Preparing for the Quantum Computing Revolution in Cybersecurity
Although the advent of quantum computing presents significant challenges to current cybersecurity frameworks, proactive measures are essential for organizations to safeguard their data.
To counter emerging quantum threats, organizations must adopt robust cybersecurity strategies that include transitioning to quantum-resistant algorithms and continuous risk assessments.
This forward-thinking approach ensures data integrity and confidentiality, empowering entities to navigate the complexities of a post-quantum cybersecurity landscape effectively.
Conclusion
In conclusion, as quantum computing advances, the urgency for robust encryption solutions is paramount. Just as knights once relied on impenetrable armor to safeguard their realms, organizations must now embrace quantum-resistant techniques to protect sensitive data. The transition to these advanced methodologies is not merely prudent but essential, ensuring that the foundations of cybersecurity remain intact amid the looming quantum revolution. Proactively addressing these challenges will be vital in maintaining data integrity and security in an increasingly complex digital landscape.